Cyberattacks on healthcare are set to intensify as critical infrastructure becomes a strategic target in an increasingly volatile geopolitical environment. According to the Global Cybersecurity Outlook 2026, cyber risk is accelerating, driven by AI, political tensions, and growing digital complexity. Yet healthcare systems struggle to keep pace, constrained by limited funding and a shortage of skilled professionals.
AI empowers hackers faster than hospitals can use it for defense
Cybersecurity has become a core pillar of national and regional security, especially as hospitals and healthcare systems are increasingly integrated into critical infrastructure. In response, the European Union introduced the NIS2 Directive (the Network and Information Security Directive 2), which sets mandatory requirements to strengthen cybersecurity across sectors such as healthcare, energy, transport, and digital infrastructure.
However, regulation alone may not be sufficient to keep pace with the rapidly evolving threat landscape. The World Economic Forum (WEF) report makes clear that artificial intelligence is reshaping cybersecurity on both sides. AI is now seen as the most significant driver of change, with 94% of respondents identifying it as the dominant force in the coming years.
AI introduces a dual dynamic: It enhances defense capabilities by enabling faster detection, automated response, and large-scale data analysis, but it expands the attack surface and allows cybercriminals to launch more sophisticated, scalable, and targeted attacks. As a result, 87% of organizations identify AI-related vulnerabilities as the fastest-growing cyber risk. The bad news is that cybercriminals are faster at adopting AI tools than hospitals that lack money and cybersecurity professionals.
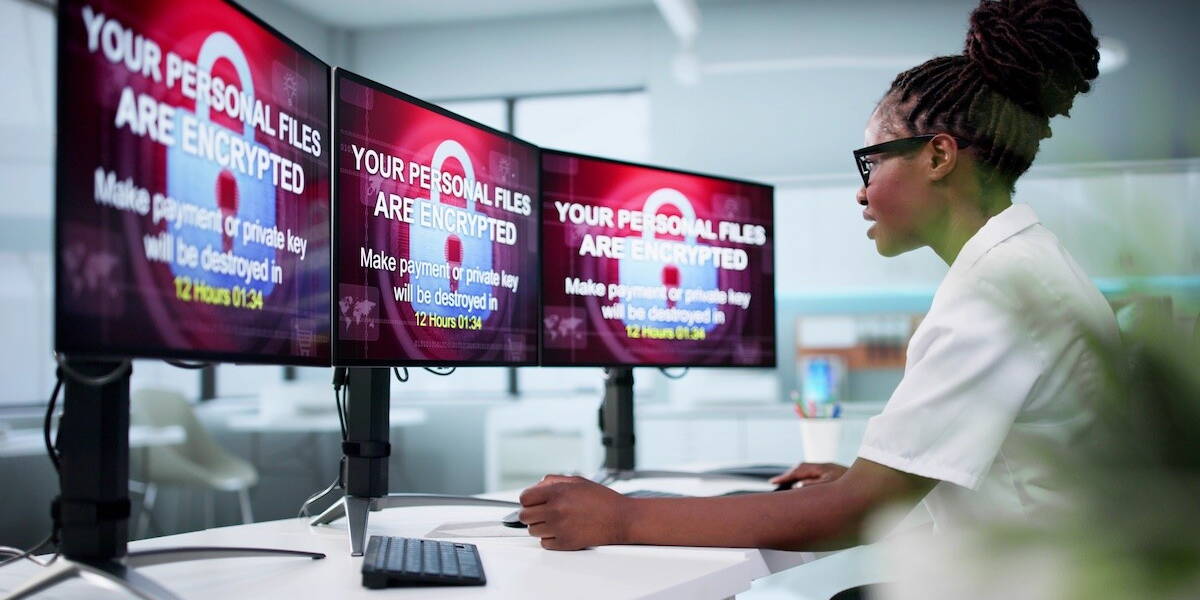
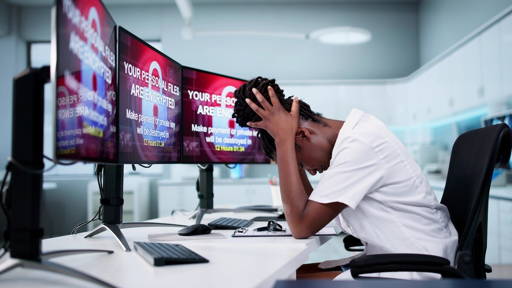
Hospitals are easy targets in the cyber war
The report highlights a sharp rise in cybercrime, with 77% of organizations reporting an increase in cyber-enabled fraud and phishing, and 73% of respondents affected either directly or through their networks.
Phishing remains the most common attack vector, but it is evolving rapidly. Generative AI enables attackers to produce highly realistic emails, impersonate medical professionals or institutions, and create deepfake audio or video. In healthcare, this translates into direct operational and clinical risks – from unauthorized access to patient records to identity theft, enabling fraudulent e-prescriptions for sedative drugs like opioids.
Healthcare systems are particularly exposed because they combine high-value data with operational urgency. Disruptions can directly impact patient care. An example is the cyberattack on Synnovis (June 2024), a laboratory services provider for NHS hospitals in London. The ransomware attack disrupted core diagnostic systems, particularly blood testing services, forcing hospitals to switch to manual processes and significantly reduce activity. Thousands of appointments and procedures were postponed, and critical services, including cancer diagnostics and blood transfusions, were affected. The disruption created bottlenecks across multiple hospitals, demonstrating how deeply healthcare delivery depends on digital infrastructure and external service providers.
The attack also led to a major data breach. Sensitive patient information, including personal identifiers and medical data, was exfiltrated and later published online. Most importantly, the incident had direct implications for patient safety, with delays in care highlighting how cyberattacks can translate into real clinical harm.
Geopolitical tensions further amplify these risks. Around 64% of organizations now consider politically motivated cyberattacks (such as infrastructure disruption or espionage) in their cybersecurity strategies. Healthcare systems, as part of the national critical infrastructure, are inevitably within this threat landscape. There is one more threat medicine is facing: disinformation campaigns. AI-driven manipulation can erode trust in healthcare institutions, spread false medical information, and influence public behavior, creating risks that extend beyond IT systems into public health
The public sector lacks the funds to adequately protect data
The WEF report highlights a significant gap in cyber resilience between the public and private sectors. Around 23% of public institutions report insufficient cybersecurity capabilities, compared to 11% in the private sector.
One of the reasons is financial. Cybersecurity talent is expensive and rare. Across Europe, cybersecurity specialists (or IT specialists) command high salaries, driven by regulatory pressure, growing threats, and a persistent talent shortage. In Germany, for example, cybersecurity professionals earn on average around €80,000–95,000 annually, with senior roles exceeding €100,000–140,000. Smaller hospitals and public healthcare providers struggle to compete for cybersecurity talent. Salaries in healthcare IT and security are typically lower and bound to rigid public-sector pay frameworks rather than market dynamics. As a result, experienced professionals gravitate toward the private sector, where higher compensation, performance-based bonuses, and clearer career paths are the norm.
However, salary alone does not explain the gap. Work in healthcare cybersecurity is often less attractive for several structural reasons. First, outdated infrastructure. Many hospitals still rely on legacy systems that were not designed with modern cybersecurity in mind. According to the WEF report, legacy systems are a major barrier to cyber resilience, increasing both complexity and risk. This makes the work more difficult, less efficient, and often more frustrating for specialists used to modern cloud-based environments.
Second, limited budgets and competing priorities. Healthcare organizations must prioritize clinical services, staffing, and patient care. Cybersecurity investments often compete with urgent medical needs, making long-term strategic investment harder to sustain.
Third, higher stakes and responsibility. In most industries, a cyberattack leads to financial or reputational damage. In healthcare, it can directly affect patient outcomes. Disruptions to systems can delay surgeries, diagnostics, or treatment decisions. This creates a unique pressure environment in which cybersecurity failures can pose risks to human life.
Fourth, complex ecosystems and dependency risks. Hospitals operate within highly interconnected digital environments, relying on external vendors, diagnostic providers, and cloud systems. This increases exposure while reducing direct control over security.
The result is a widening talent gap. As the WEF report highlights, a lack of cybersecurity skills is one of the main barriers to strengthening cyber resilience and to implementing advanced technologies, such as AI, in security operations.
The Global Cybersecurity Outlook 2026 concludes that cybersecurity is now a strategic imperative. It underpins operational continuity, patient safety, and trust in healthcare systems. The report emphasizes the need to move from reactive to proactive approaches. This includes strengthening cyber resilience through structured incident response planning, continuous monitoring, regular testing, and closer cross-sector and cross-border collaboration. While it all sounds logical, healthcare managers have limited budgets for IT and cybersecurity. They are torn between the pressure to implement new, sophisticated AI-driven tools, not to lag behind technological progress, and the need to ensure a legitimate level of cybersecurity.
There is no perfect balance between digital progress and data protection, and more money does not always translate into better cybersecurity, as overburdened healthcare workers are susceptible to social engineering tactics that gain access to data.